Proxies are used for discoveries in network zones where the main vScope might not have full access to all relevant ports, such as a DMZ, a customer network, or another closed network. vScope proxies communicate with the main vScope over one single port.
You can use as many proxies as you wish.
1. Prepare a server (in the closed network zone) where the discovery proxy shall run
- Dedicate a server in the network zone where the discovery proxy is intended to run
- You can run the vScope Discovery proxy on a dedicated server or locate the proxy on an already existing server located in the intended zone
Requirements
- Windows OS*
- 6 GB RAM (Dedicate 4GB to vScope)
- 60 GB HDD
- No additional database is required.
- 2 CPU Cores
*vScope can run on Linux OS too, but the Linux version only supports the discovery of Windows systems through Win-RM (not WMI)
2. Install the proxy
- Download the proxy installer package on the intended discovery proxy server:
- Download for Windows OS (for Linux, please follow this guide)
- Run the installer
- Point the Host address (either an IP address or a DNS-resolvable address) towards the master vScope.
- Specify a communication port between the proxy and the master. The default port is TCP 4445, but you can select any port of your choice.
- Finish the installer and let the proxy start.
- The proxy will now identify itself with the master automatically (it might take a few minutes).
Important notice
Any discovery setting such as dynamic threading or RAM setting on the master vScope is not automatically distributed to the proxy installation. These settings are configured on the proxy in the same way as on the master vScope:
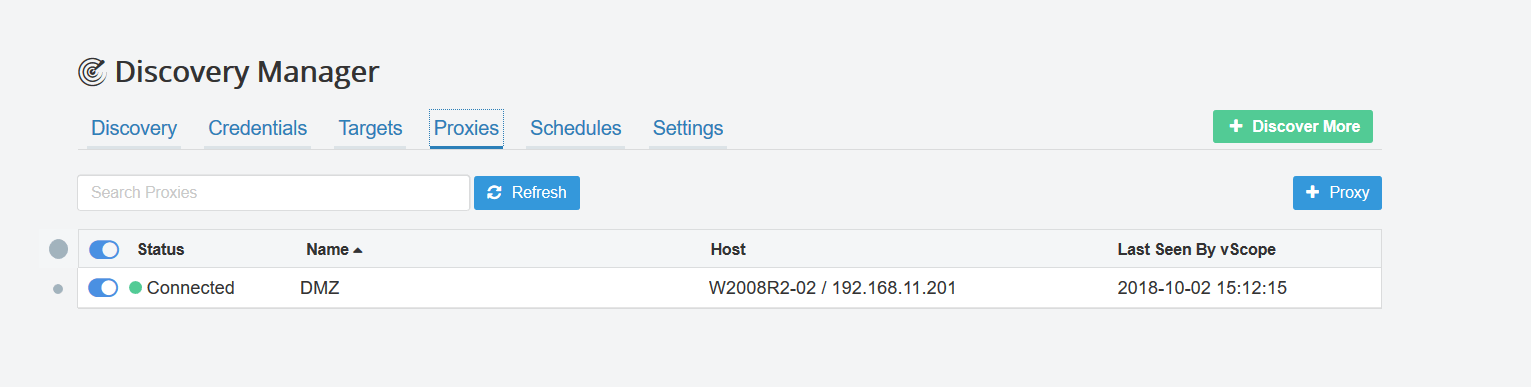
3. Locate the proxy in the Discovery Manager
- Open vScope and log in
- Go to the Discovery Manager and select the Proxies tab
- You should now see the proxy being listed
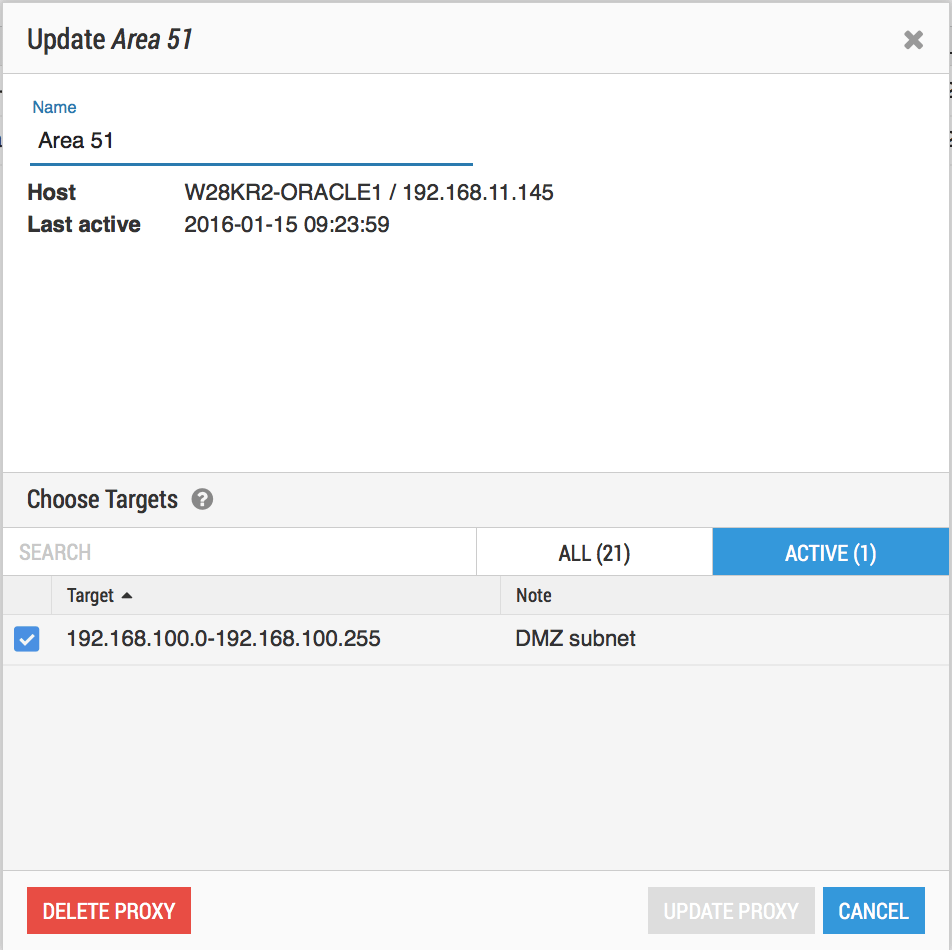
- If you wish, you can rename your proxy to a friendly name, such as “DMZ”, “Area 51”, or “Customer Inc. Zone”
- On this page, you can also temporarily disable proxies and see the status of them
Note – Proxy does not show up in vScope
Ensure that ports are not blocked on either side (eg. Windows Defender).
4. Assign a target or target range to a proxy
- In this final step, you instruct the proxy where to run discovery.
- When a target, or target range, is assigned to a proxy, vScope will delegate the discovery of that target to the proxy
- The proxy will use the credentials specified for the selected target an for any other target